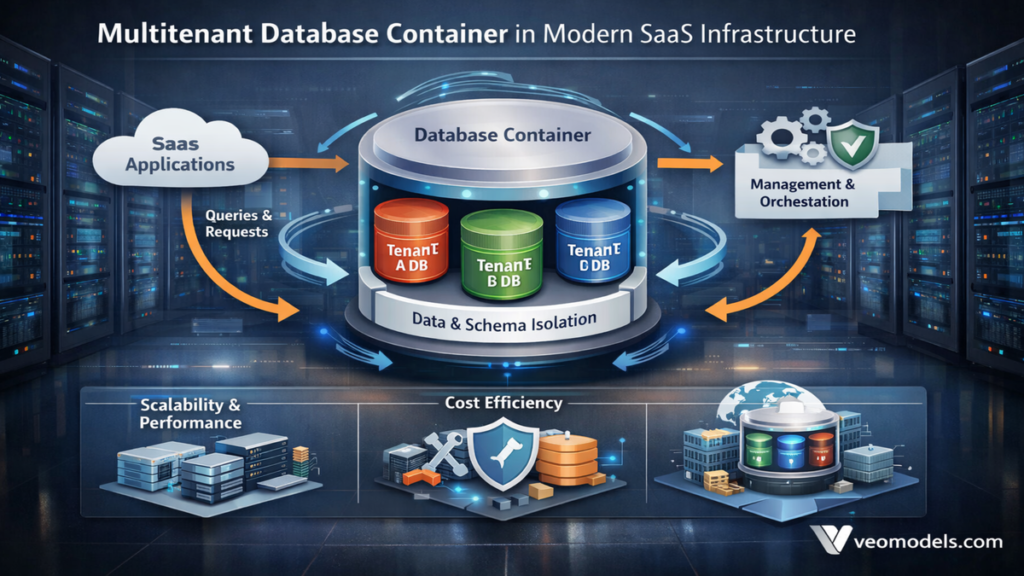
When engineering teams design scalable SaaS platforms, one architectural question inevitably surfaces early: how do we isolate customers while keeping infrastructure efficient? Multitenant database containers provide one answer. These architectures host multiple logically isolated tenant databases within a single shared container system, allowing providers to optimize compute, storage, and operational overhead without fully dedicating hardware per client.
In practical deployments across cloud-native environments, multitenant database containers rely on a container database that manages shared resources, alongside pluggable or tenant-specific databases that maintain logical separation. Vendors such as Oracle introduced the CDB and PDB model in Oracle Database 12c in 2013, while SAP HANA implemented Multitenant Database Containers in SPS09 (2014). Today, similar patterns appear in PostgreSQL clusters, distributed systems such as Citus, and Kubernetes-managed database operators.
I have worked with platform teams evaluating tenant isolation strategies for AI-powered SaaS products, and I have seen firsthand how architectural decisions at this layer influence cost, security, and long-term maintainability. This article explores the technical foundations, operational tradeoffs, and real-world deployment patterns shaping multitenant containerized databases across modern cloud ecosystems.
The Core Architecture of Shared Container Databases
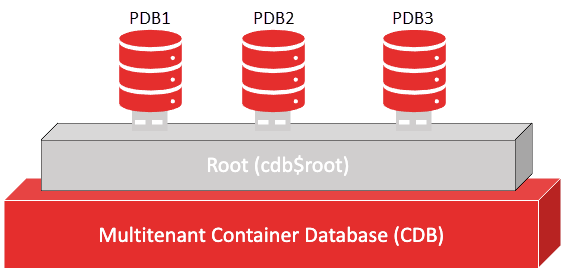
At the center of this model sits the Container Database, or CDB, which governs shared services such as memory allocation, transaction logs, and backup orchestration. Within it reside Pluggable Databases, or PDBs, each representing a logically isolated tenant.
Oracle Database 12c formalized this structure in 2013, enabling administrators to manage multiple databases as one consolidated unit (Oracle, 2013). SAP HANA’s MDC introduced a comparable tenant isolation model in 2014, allowing each tenant to appear operationally independent despite shared infrastructure.
The distinction between logical and physical isolation defines the architecture’s strength. Tenants share compute and storage pools, yet maintain distinct schemas, users, and metadata boundaries. In Kubernetes-native environments, namespaces and resource quotas extend this pattern, limiting CPU and memory consumption per tenant.
In deployment reviews I have observed, the CDB-PDB approach consistently reduces hardware sprawl, but demands careful governance to prevent cross-tenant performance interference.
Resource Efficiency Versus the Noisy Neighbor Risk
Multitenancy exists primarily to improve resource efficiency. Instead of provisioning dedicated servers for each customer, providers pool infrastructure.
| Aspect | Benefits | Drawbacks |
|---|---|---|
| Cost and Scaling | Reduced overhead through shared memory and storage | Risk of performance contention |
| Provisioning | Rapid onboarding via template cloning | Resource overcommitment possible |
| Maintenance | Centralized patching and upgrades | Coordination complexity |
| Infrastructure Footprint | Lower total hardware usage | Requires monitoring precision |
The challenge is the so-called noisy neighbor effect. If one tenant executes intensive workloads, others may experience degraded performance.
In 2020, AWS highlighted resource contention mitigation strategies within Amazon RDS and Aurora, emphasizing workload isolation through auto-scaling and monitoring (AWS, 2020). The principle remains universal: multitenant efficiency requires intelligent workload governance.
In AI-driven SaaS environments, where some tenants may process high-volume inference or voice data, workload unpredictability amplifies the importance of quotas and adaptive scaling policies.
Isolation Strategies in Multitenant Database Containers
Logical separation mechanisms define the security baseline of multitenant systems. Most implementations rely on schema-per-tenant or database-per-tenant approaches within the container.
Row-Level Security, formalized in PostgreSQL 9.5 in 2016, enforces query filtering at the database layer. By attaching tenant identifiers to records and policies, systems prevent unauthorized cross-tenant data access.
As database expert Bruce Momjian has noted, “Row-level security allows policies to be attached directly to tables, making enforcement consistent and centralized” (Momjian, 2016).
Namespaces in Kubernetes extend isolation beyond the database itself. Resource quotas limit CPU and memory allocation, preventing runaway workloads.
From my experience reviewing SaaS architectures, combining RLS with namespace-level constraints yields more predictable isolation outcomes than relying on schema separation alone.
Security and Compliance Considerations
Security concerns extend beyond logical isolation. Encryption at rest and in transit remains essential.
The National Institute of Standards and Technology updated its cryptographic guidance in 2023, reaffirming AES-256 as a widely accepted encryption standard (NIST, 2023). Most enterprise database systems integrate AES-based encryption for storage volumes.
Role-Based Access Control further restricts administrative boundaries. Each tenant may receive distinct service accounts, minimizing lateral access risks.
Network segmentation, especially in Kubernetes clusters, isolates traffic between namespaces. Policies define which pods may communicate.
In regulated industries such as healthcare or finance, compliance frameworks including SOC 2 and ISO 27001 require auditability. Centralized logging within the container database simplifies evidence collection for security audits.
Security in multitenant systems is layered rather than singular.
Scalability and Automated Tenant Provisioning
Automation underpins the operational success of multitenant architectures. Manual onboarding quickly becomes untenable as tenant counts grow.
| Practice | Benefit | Tools |
|---|---|---|
| Auto-scaling PDBs | Dynamic resource allocation | Oracle AutoPDB, Kubernetes HPA |
| Centralized Backups | Unified disaster recovery | CDB snapshots |
| Infrastructure as Code | Automated tenant creation | Terraform, CloudFormation |
| Observability | Early anomaly detection | Prometheus, Grafana |
In distributed PostgreSQL clusters such as Citus, shard-based partitioning allows tenant distribution across nodes. DynamoDB offers tenant-key partitioning for schemaless architectures.
I have seen onboarding APIs reduce tenant provisioning from hours to seconds. Infrastructure as code eliminates configuration drift, which is especially important in AI SaaS systems where data ingestion patterns evolve rapidly.
Scalability in this context means predictable growth without operational fragility.
Kubernetes and Container-Native Deployment Patterns
Modern SaaS platforms often deploy databases within Kubernetes clusters using operators.
Database operators automate lifecycle management, including scaling, failover, and updates. Kubernetes namespaces act as logical tenant partitions at the infrastructure layer.
The Cloud Native Computing Foundation reported in 2023 that over 70 percent of organizations use Kubernetes in production (CNCF, 2023). As container orchestration becomes standard, database multitenancy increasingly aligns with cluster-native governance patterns.
By combining namespace isolation with database-level RLS policies, teams create defense-in-depth protection. Resource quotas reduce the likelihood of contention spikes.
In AI-driven SaaS deployments, particularly those handling inference logs or voice metadata, container-native multitenancy simplifies horizontal scaling while preserving tenant boundaries.
Comparing Multitenant and Single-Tenant Architectures
Not all SaaS applications adopt multitenancy. Some prefer dedicated database instances per customer.
| Dimension | Multitenant | Single-Tenant |
|---|---|---|
| Infrastructure Cost | Lower | Higher |
| Customization | Moderate | High |
| Isolation Strength | Logical | Physical |
| Maintenance Complexity | Centralized | Distributed |
| Scaling Speed | Faster provisioning | Slower setup |
Single-tenant models provide stronger physical isolation but incur higher operational cost. Multitenant systems reduce redundancy while demanding stricter monitoring discipline.
In AI analytics platforms where datasets are large but structurally similar across clients, shared infrastructure often makes economic sense. However, financial institutions handling highly sensitive data may prefer dedicated clusters.
Architectural choice reflects risk tolerance, regulatory exposure, and cost objectives.
Observability and Performance Monitoring
Effective monitoring distinguishes successful multitenant deployments from fragile ones.
Prometheus-based metrics per namespace allow granular visibility into CPU usage, query latency, and memory pressure. Grafana dashboards visualize anomalies before they escalate.
Google’s Site Reliability Engineering framework emphasizes proactive monitoring as a reliability cornerstone (Beyer et al., 2016). Multitenant systems amplify this need because performance fluctuations ripple across tenants.
In several cloud infrastructure assessments I conducted, inadequate observability proved more damaging than flawed isolation models. Without visibility, administrators cannot differentiate systemic issues from tenant-specific spikes.
Observability ensures fairness and predictability.
Designing for AI-Driven SaaS Applications
AI-powered SaaS platforms introduce unique data patterns. Chatbots, voice processing pipelines, and inference logging create uneven storage and compute demands.
Multitenant database containers accommodate these workloads when paired with tenant-level quotas and dynamic scaling. PostgreSQL with schema isolation and row-level security provides structured governance. DynamoDB supports partition-based tenant separation for high-velocity key-value workloads.
In practical DevOps environments, combining Kubernetes namespaces, database RLS policies, and encryption controls creates a layered security posture.
The key insight is alignment. Infrastructure must match application behavior. For AI SaaS startups scaling rapidly, multitenant container models offer flexibility without excessive overhead, provided that governance mechanisms remain robust.
Takeaways
- Multitenant database containers centralize management while preserving logical tenant isolation.
- CDB and PDB models optimize infrastructure efficiency for SaaS platforms.
- Isolation requires row-level security, namespace quotas, and encryption.
- Automation streamlines tenant onboarding and reduces operational risk.
- Observability prevents noisy neighbor performance degradation.
- Architecture choice depends on regulatory exposure and workload variability.
Conclusion
I see multitenant database design as one of the foundational infrastructure decisions in SaaS engineering. It shapes cost efficiency, compliance posture, and operational resilience. While the architecture introduces complexity around isolation and monitoring, its benefits are substantial when managed correctly.
As AI-driven services expand across industries, the need for scalable, secure tenant separation intensifies. Logical isolation paired with encryption, observability, and automated governance provides a balanced path forward.
Ultimately, the success of multitenant systems depends less on technology selection and more on disciplined implementation. Teams that invest early in isolation policies, monitoring, and automation build platforms capable of scaling without compromising trust.
Read: GitHub Infrastructure Power and Microsoft’s Strategic Bet
FAQs
1. What is a container database?
A container database manages shared infrastructure resources while hosting multiple logically isolated tenant databases within it.
2. How do pluggable databases work?
Pluggable databases operate as independent tenant environments inside a container database, maintaining separate schemas and users.
3. Is multitenancy secure enough for regulated industries?
Yes, when combined with encryption, RBAC, row-level security, and monitoring controls.
4. What causes the noisy neighbor effect?
Resource contention occurs when one tenant consumes disproportionate CPU or memory, affecting others.
5. Can Kubernetes improve tenant isolation?
Yes. Namespaces and resource quotas enhance isolation at the infrastructure level.
References
Amazon Web Services. (2020). Managing performance in Amazon RDS environments. https://aws.amazon.com
Beyer, B., Jones, C., Petoff, J., & Murphy, N. R. (2016). Site reliability engineering. O’Reilly Media.
Cloud Native Computing Foundation. (2023). CNCF annual survey 2023. https://www.cncf.io
Momjian, B. (2016). PostgreSQL row-level security. PostgreSQL Documentation. https://www.postgresql.org
National Institute of Standards and Technology. (2023). Advanced Encryption Standard (AES). https://csrc.nist.gov
Oracle. (2013). Oracle Database 12c Release 1 new features guide. https://docs.oracle.com